Security by Design Security has long been treated as something that sits alongside software: a
APIs Integral to a Successful DDI Strategy
APIs Integral to a Successful DDI Strategy Network engineering teams should pay close attention to
Transforming the SDLC: How UST Enables AI-Native Software Delivery at Enterprise Scale
Transforming the SDLC: How UST Enables AI-Native Software Delivery at Enterprise Scale CIOs, CTOs, and
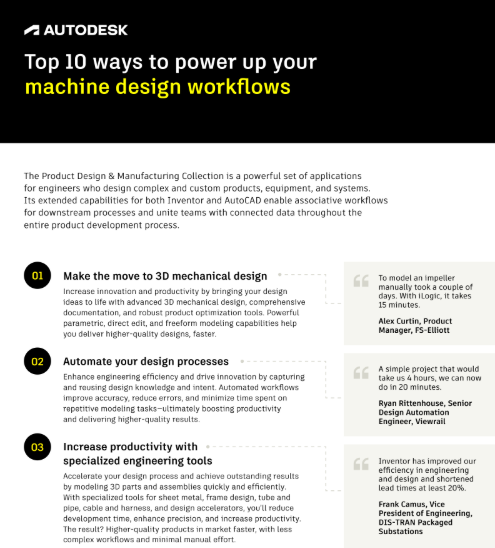
Top 10 ways to power up your machine design workflows
Top 10 ways to power up your machine design workflows The Product Design & Manufacturing
People like you are transforming T&E with Soldo
People like you are transforming T&E with Soldo Travel and expenses aren’t going away, but
Tailspend running wild?
Tailspend running wild? Chances are, you’ve come across a similar scenario in procurement. Tail spend,
From Integration to Intelligence: How Agentic
From Integration to Intelligence: How Agentic What’s the optimal path to agentic artificial intelligence (AI)
2025 Gartner Magic Quadrant for Data Integra
2025 Gartner Magic Quadrant for Data Integra By 2027, AI assistants and AI-enhanced workflows within
AI-Ready Data Ecosystems: Succeed and Sc
AI-Ready Data Ecosystems: Succeed and Sc AI workloads demand speed, but also accuracy and trust.
Distributed Denial-of-Service (DDoS) ProtectionReviews, Tips and Advice from Real Users
Distributed Denial-of-Service (DDoS) Protection Reviews, Tips and Advice from Real Users Distributed Denial‐of Service (DDoS)